Risk Pattern Evaluation of 18008493574 and Activity
The analysis of 18008493574 and its activity emphasizes deviations from established baselines, focusing on phishing signals and credential reuse as salient markers. Timing and cadence anomalies are noted, with uncommon intervals and repetitive actions suggesting evasion attempts. Cross-domain signals, including device and location context, enable signal fusion for risk inference. The framework aims for governance-aligned detection and proactive containment, but the implications hinge on integrating continuous monitoring with actionable mitigations that remain to be clarified.
What the Risk Pattern of 18008493574 Reveals About Baseline Activity
The risk pattern associated with 18008493574 offers a concise lens into baseline activity by isolating deviations from expected operational norms.
The analysis identifies phishing indicators and credential reuse as salient markers, enabling precise normalization of normal traffic.
Findings emphasize reproducible thresholds, enabling quick flagging of anomalies while preserving system freedom to operate within defined risk tolerances.
How Timing and Frequency Signal Intent and Potential Manipulation
Timing and frequency patterns provide a granular signal for intent and potential manipulation by contrasting cadence against baseline workflows.
Analysis reveals timing patterns that cluster around uncommon intervals, suggesting deliberate sequencing.
Frequency signals show elevated repetition of specific actions beyond expected norms, increasing risk of circumvention.
The data indicate measurable deviations warranting methodological scrutiny and continued monitoring to deter exploitative behavior.
Contextual Signals: Correlating Events, Devices, and Locations to Risk
Contextual signals integrate cross-domain observations to strengthen risk inference by correlating events with associated devices and locations.
The analysis treats burst pattern occurrences as cross-referenced indicators, examining timing, geography, and device cross-ownership to quantify risk elevation.
Device correlation across sessions reveals clustering, while location triangulation enables anomaly detection.
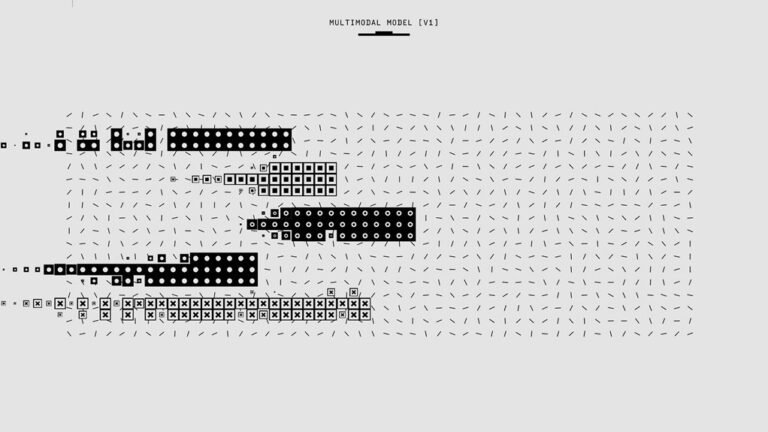
Signal fusion, device mapping
From Detection to Defense: Actionable Steps to Monitor and Mitigate Risk
From detection to defense, the chapter delineates a structured, data-driven approach to monitor risk signals and implement mitigations with measurable impact. It details a framework for Identifying anomalies and Correlating events across systems, channels, and times, enabling timely alerts and prioritized responses.
The emphasis remains rigorous, actionable, and transparent, aligning monitoring cadence with governance, and sustaining freedom through proactive risk containment.
Conclusion
The examination reveals a baseline labyrinth where 18008493574’s activity threads through predictable corridors yet periodically veers into anomalous cadences. Timing and frequency signals act as precision instruments, exposing manipulative intent beneath a veneer of normalcy. Contextual signals weave cross-domain threads—devices, locations, ownership—into a complex risk tapestry. From detection to defense, the data-driven framework translates signals into actionable mitigations, maintaining governance-aligned cadence while curbing circumvention. In this forest of indicators, vigilance remains the compass and shield.