In-Depth Caller Investigation of 9126165004 and Alerts
The discussion centers on an in-depth caller investigation of the number 9126165004, framed by structured log review and verification protocols. It emphasizes identity confirmation, pattern recognition, and cross-source correlation to separate legitimate contact from anomalies. Data from network logs, geolocation, and device fingerprints are analyzed for coherence and threat signals. Timely alerts are positioned as catalysts for containment and accountability, leaving critical questions open and urging further examination.
What a Caller Investigation Involves: Setting the Stage for 9126165004
A caller investigation of 9126165004 begins with a structured assessment of available data, including call logs, time stamps, and caller identifiers, to establish a factual baseline.
The process emphasizes caller identity and pattern verification, while organizing correlation data and alerts timing to support objective evaluation.
Outcomes focus on security considerations, reproducibility, and transparent methodology for informed freedom-focused interpretation.
How Investigators Verify Caller Identities and Patterns
In turning from the prior assessment of data collection, investigators methodically verify caller identities and patterns by cross-referencing multiple data streams. They apply caller verification protocols to authenticate numbers, timestamps, and routing data, isolating anomalies. The process catalogues threat patterns, flags unusual call frequencies, and assesses contextual cues, maintaining objectivity. Results inform risk assessment while preserving due process and operational transparency.
Correlating Data Across Sources to Distinguish Threats
Correlating data across multiple sources enables investigators to separate genuine threats from benign activity by aligning caller records, network logs, and contextual metadata.
The process emphasizes rigorous data correlation, cross-referencing timestamps, geolocation, and device fingerprints to reveal coherent threat patterns.
The Value of Timely Alerts: Outcomes for Organizations and Individuals
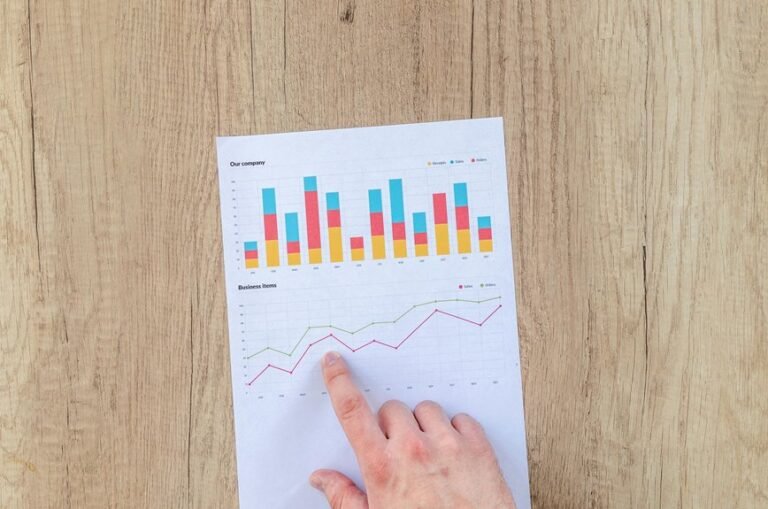
Timeliness in alerting shapes both organizational resilience and individual safety by accelerating response workflows, enabling rapid containment of threats, and reducing potential damage.
This analysis evaluates how timely alerts influence investigative outcomes, emphasizing systematic caller verification and disciplined data correlation.
When verification chains are robust, organizations can allocate resources efficiently, minimize false positives, and achieve clearer, more actionable intelligence for stakeholders and affected communities.
Conclusion
In a detached, analytical frame, the investigation of 9126165004 demonstrates how disciplined data correlation and verification protocols yield clear threat signals and defensible decisions. By cross-referencing logs, geolocation, and device fingerprints, investigators distinguish benign activity from malicious patterns, enabling timely containment. An anticipated objection—privacy concerns—can be offset by due-process safeguards and transparent reporting that preserve trust. The result is objective risk assessment, reproducible reasoning, and organizational resilience amid evolving communication threats.