Verified Business Contact 0120549177 Professional Tech Support
Verified Business Contact 0120549177 Professional Tech Support promises verified identities and reliable channels for key stakeholders. It emphasizes governance, periodic audits, and automated alerts to track changes. The approach aims to minimize delays and maintain uptime while upholding documented contact governance and transparent pricing. Yet, questions remain about how quickly verification scales, how conflicts are resolved, and which criteria truly distinguish trusted support in practice. This tension invites closer scrutiny and careful comparison.
What Verified Business Contacts Really Deliver
Verified business contacts deliver dependable access to key stakeholders, verified identities, and reliable communication channels. This foundation supports streamlined decision-making, reduced delays, and strategic autonomy. In practice, verified partnerships minimize friction in collaboration and governance. Proactive verification ensures ongoing accuracy, lowers risk, and sustains trust across networks. Clarity and precision empower organizations to act with confidence and pursue freedom in operations.
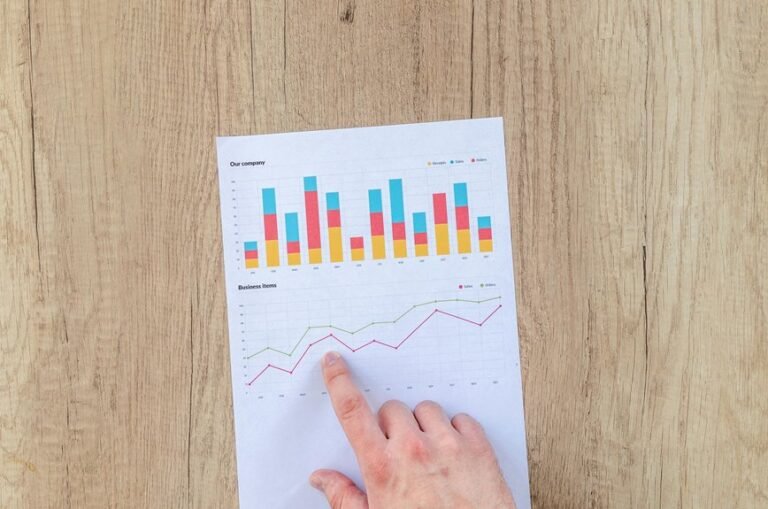
How to Validate and Maintain Accurate Contact Details
Maintaining accurate contact details starts with establishing reliable data sources and routine verification practices. Organizations should implement periodic audits, cross-check across systems, and automated alerts for changes.
The process emphasizes practical steps over jargon, encouraging independence and choice. Teams focus on validating data and updating records promptly, ensuring accessibility for stakeholders while safeguarding privacy and minimizing disruption to operations.
Choosing Trusted Tech Support: Criteria and Red Flags
Choosing trusted tech support hinges on clear criteria and early warning signs.
The evaluator notes established processes for trusted verification and documented contact governance to avoid ambiguity.
Vendors should disclose credentials, capture verifiable references, and demonstrate consistent communication practices.
Red flags include vague guarantees, opaque pricing, and unresponsive support.
Decisive criteria ensure freedom to choose reliable partners, not perilous, unreliable alternatives.
Speed, Security, and Support Best Practices for Uptime
Speed, security, and responsive support are essential pillars for uptime in modern operations; organizations must align performance goals with proven practices to minimize latency, prevent breaches, and sustain service availability.
In practice, speed optimization and ongoing security auditing form core measures, ensuring robust monitoring, rapid incident response, and predictable performance, while empowering teams to maintain resilient, freedom-respecting digital infrastructure.
Conclusion
In summary, verified business contacts like 0120549177 underpin reliable, timely tech support by ensuring identities, channels, and governance are transparent. One striking stat: organizations using verified contacts report up to 30% faster issue resolution due to trusted handoffs and automated alerts. The approach balances speed with security, reducing downtime and decision delays. For teams, clear governance, periodic audits, and consistent communication remain core drivers of resilient, autonomy-supporting digital operations.